OverTheWire Vortex — Complete Walkthrough Index
OverTheWire Vortex — Complete Walkthrough Index
Halloo SuiiKawaii dessu!! Glad to see you again. This page is the master index for my Vortex walkthroughs — actually i don’t have much to say because the title and desciption already help you figure out what is this post about so yeah today we gonna do some OverTheWire Vortex 🗣️🔥🔥🔥🔥!!

Introduction
If you’re getting into cybersecurity or ethical hacking, OverTheWire (open in new tab) is one of the best beginner-friendly playgrounds.
Vortex is a classic pwn/RE wargame: socket programming, format strings, NX stack hurdles, heap/PHKmalloc, keygen/reverse, RNG seeding — the whole buffet. It’s perfect for building low-level instincts you’ll reuse in CTFs and real-world exploit dev.
Why play Vortex?
- Hands-on with binaries, sockets, and tricky mitigations.
- Mix of RE + exploitation across many patterns.
- Trains careful reading of specs & source.
- Totally free — just a terminal + internet.
By the end you’ll be comfortable with:
- Disassembling/inspecting ELF binaries.
- Reasoning about memory layouts, canaries, NX, heap allocators.
- Building tiny clients to speak custom services.
About This Series
Each level has its own post with:
- Login Info — how to connect for that level
- Task — the original OTW prompt
- Theory — short notes on the commands/concepts
- Solution — step-by-step, reproducible walkthrough
My goal isn’t to dump passwords but to show why each step works so you can solve similar problems on your own.
How to Play Vortex (and actually learn)
- Read the challenge carefully.
- Try first, then peek at hints if stuck.
- Use
man/--helpaggressively. - Keep a logbook of commands, ideas, dead ends.
- Fail fast, retry until you can solve it without notes.
Pro tip: craft tiny TCP clients and keep your disassembler/debugger open — small RE loops beat guesswork.
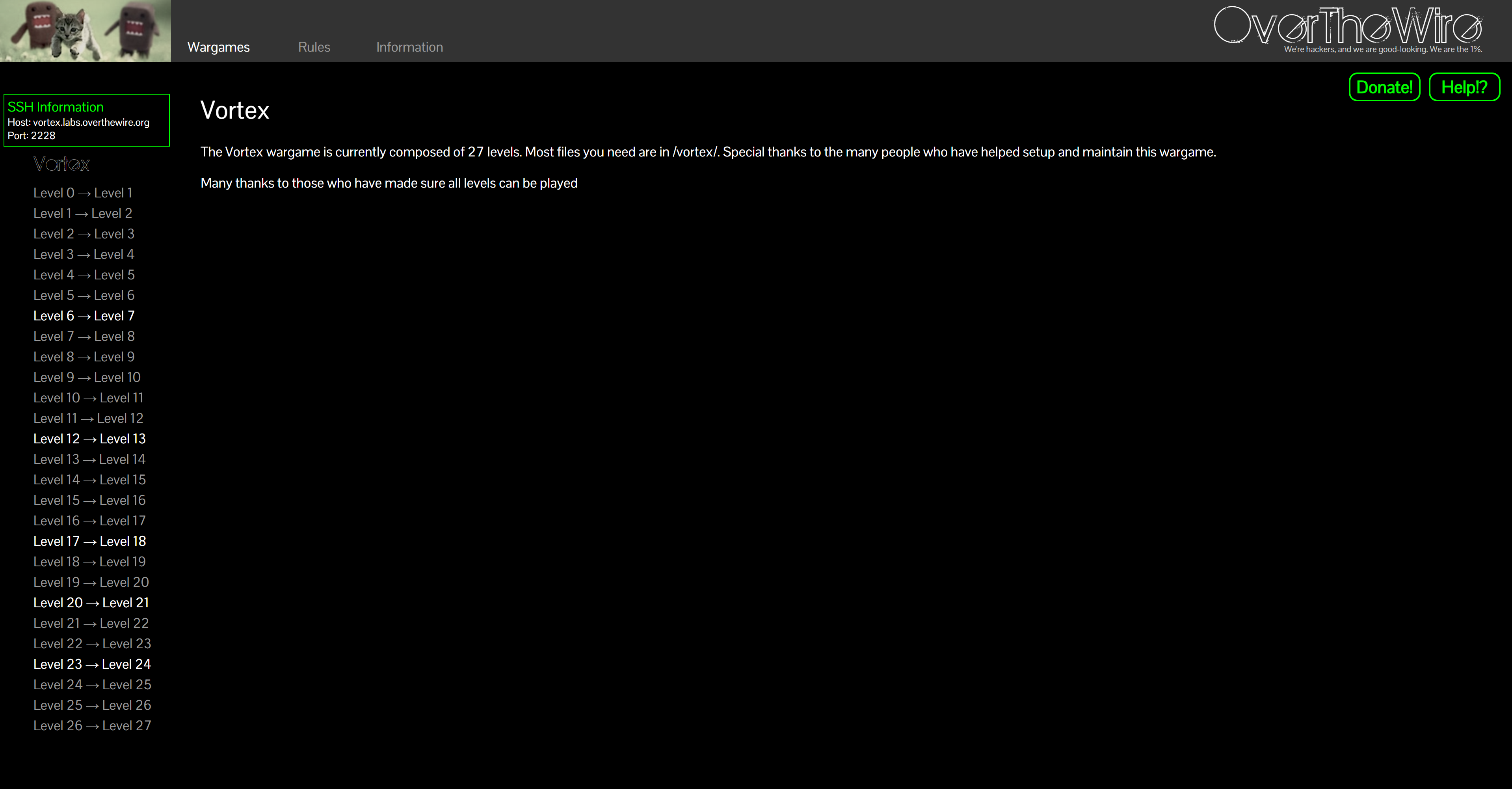
Levels Index (0 → 26 → 27)
Each link opens in a new tab. The one-liner tells you the main idea for that level.
-
🐣 Level 0 — Socket Sum Warm-up
Read post → — Setup & client skeleton for Vortex. -
🔢 Level 0 → 1 — Read 4 uint32 & Sum
Read post → — Connect to port 5842, add 4 little-endian integers. :contentReference[oaicite:0]{index=0} -
🐥 Level 1 → 2 — Canary Values
Read post → — Find a specific value inptr; mind EOF handling. :contentReference[oaicite:1]{index=1} -
📦 Level 2 → 3 — “Special” tar
Read post → — Craft a tar that trips the checker. :contentReference[oaicite:2]{index=2} -
🧱 Level 3 → 4 — Stack Overflow (setuid)
Read post → — Overflow withsetuid/ctors detail. :contentReference[oaicite:3]{index=3} -
🧵 Level 4 → 5 — Format String
Read post → — Classic%bug; argc check twist. :contentReference[oaicite:4]{index=4} -
🔐 Level 5 → 6 — MD5 Brute-force
Read post → — 5-char [A-Za-z0-9] search space. :contentReference[oaicite:5]{index=5} -
🛠️ Level 6 → 7 — Generic Binary Exploitation
Read post → — Disassemble to find the hole. :contentReference[oaicite:6]{index=6} -
🧮 Level 7 → 8 — CRC32 Target
Read post → — MakeCRC32(argv[1]) == 0xe1ca95ee. :contentReference[oaicite:7]{index=7} -
🔍 Level 8 → 9 — Simple RE
Read post → — Disassemble a dyn-linked binary. :contentReference[oaicite:8]{index=8} -
⚫ Level 9 → 10 — BlackBox
Read post → — No info — log in & poke around. :contentReference[oaicite:9]{index=9} -
🎲 Level 10 → 11 — RNG Seed
Read post → — Read 20 ints; recover PRNG seed in 30s. :contentReference[oaicite:10]{index=10} -
📚 Level 11 → 12 — Heap (phkmalloc) Chunk Corruption
Read post → — Corrupt the heap for control. :contentReference[oaicite:11]{index=11} -
🚫 Level 12 → 13 — NX Stack (I)
Read post → — Exploit with non-exec stack constraint. :contentReference[oaicite:12]{index=12} -
🧠 Level 13 → 14 — NX Stack (II)
Read post → — How big is your shellcode? :contentReference[oaicite:13]{index=13} -
🧪 Level 14 → 15 — Bad Encryption (traffic trace)
Read post → — Analyze weak crypto over TCP. :contentReference[oaicite:14]{index=14} -
🔓 Level 15 → 16 — Weak Encryption (file)
Read post → — Decrypt 8-byte A–Z password. :contentReference[oaicite:15]{index=15} -
🧮 Level 16 → 17 — “The BOFH”
Read post → — Recover 100 of 128 key bits. :contentReference[oaicite:16]{index=16} -
↩️ Level 17 → 18 — Working Backwards
Read post → — Reverse the flow, then exploit. :contentReference[oaicite:17]{index=17} -
🎰 Level 18 → 19 —
urandomSeeds
Read post → — Abuse weak randomness. :contentReference[oaicite:18]{index=18} -
🗝️ Level 19 → 20 — Keygen
Read post → — Keygen with weak encryption hurdle. :contentReference[oaicite:19]{index=19} -
🔢 Level 20 → 21 — Remote Integer Fun
Read post → — Exploit integer handling remotely. :contentReference[oaicite:20]{index=20} -
🔁 Level 21 → 22 — Reverse Me (harder)
Read post → — Understand the encryptor & bypass. :contentReference[oaicite:21]{index=21} -
🧩 Level 22 → 23 — Object Analysis (keygen)
Read post → — Inspect/vortex/vortex22_*.o. :contentReference[oaicite:22]{index=22} -
🪞 Level 23 → 24 — Mirror Properties
Read post → — Research prompt is the hint. :contentReference[oaicite:23]{index=23} -
🌱 Level 24 → 25 — Guess the Seed
Read post → — Study GLIBCrandom_r.c. :contentReference[oaicite:24]{index=24} -
🕳️ Level 25 → 26 — Crackploit (missing)
Read post → — Level lost; kept for history only. :contentReference[oaicite:25]{index=25} -
🏁 Level 26 → 27 — Vortex Complete
Read post → — “Create your own challenge” (historical). :contentReference[oaicite:26]{index=26}
Conclusion
There are tons of guides out there from other Blog to Youtube videos, but i made this series is my take with my own style of workflow, notes, and explanations. Even if you just skim, I hope it will helps you learn faster.
Finishing Vortex feels like leveling up your RE + pwn toolkit 🧠:
- Syscalls, RNG, and memory bugs stop being scary.
- You can build tiny tools to speak weird services.
- You can learn anything by slicing it into tiny, winnable steps.
Next adventures:
- Krypton (crypto)
- Narnia (binary exploitation)
- Labs: TryHackMe / Hack The Box
Keep playing, keep breaking (legally!), keep notes — you got this 💪
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


