OverTheWire Utumno — Complete Walkthrough Index
OverTheWire Utumno — Complete Walkthrough Index
Halloo SuiiKawaii dessu!! Glad to see you again. This page is the master index for my Utumno walkthroughs — actually i don’t have much to say because the title and desciption already help you figure out what is this post about so yeah today we gonna do some OverTheWire Utumno 🗣️🔥🔥🔥🔥!!
Introduction
If you’re diving into binary exploitation or low-level security challenges, OverTheWire (open in new tab) is a fantastic playground.
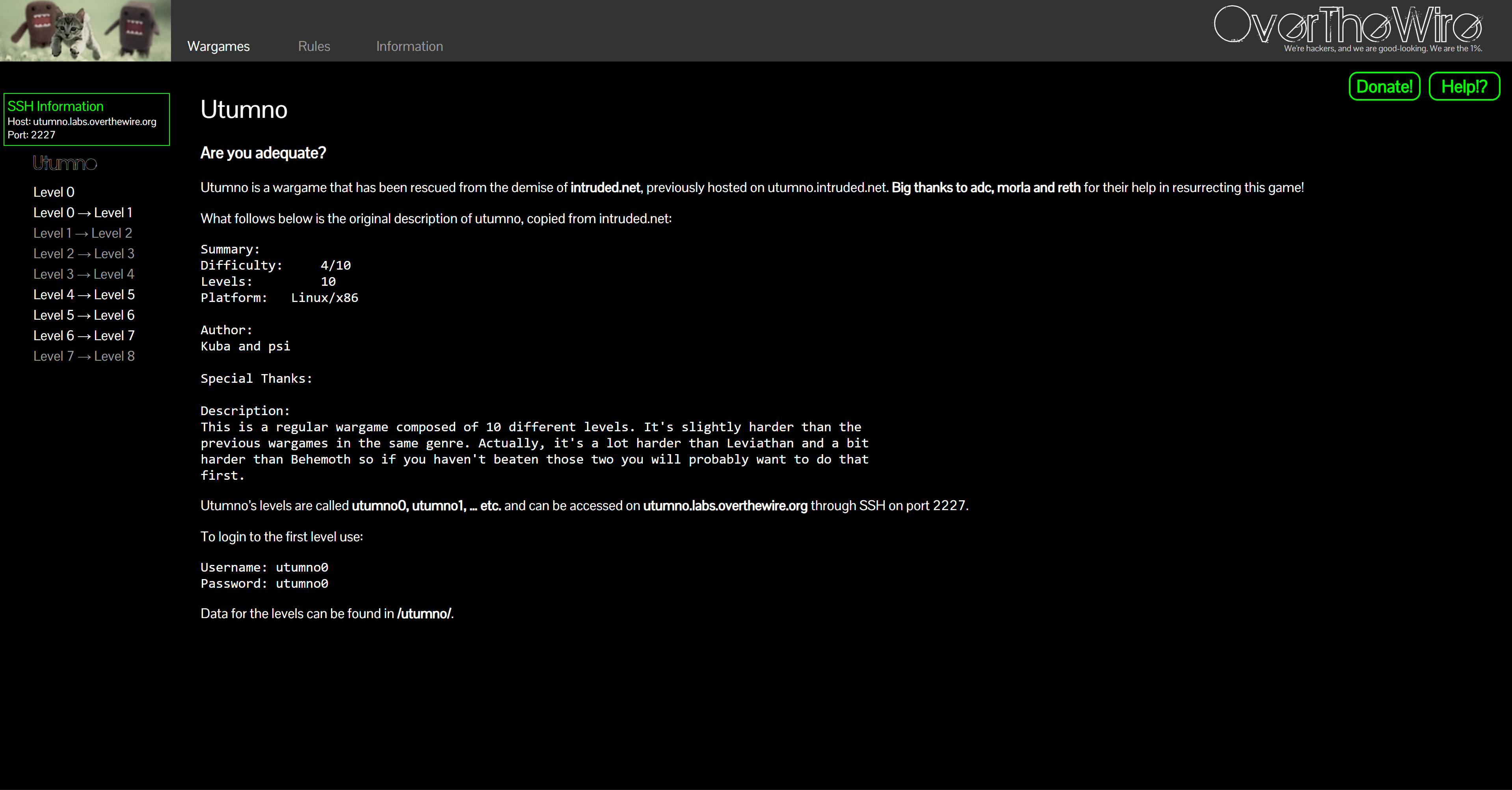
Utumno focuses on stack-based exploitation. Compared to Bandit (Linux basics), Narnia (intro exploitation), or Behemoth (weird logic bugs), Utumno steps it up with harder stack smashing, function pointer overwrites, and memory tricks. It’s tough but super rewarding.
Why play Utumno?
- Learn real exploit techniques in a safe lab.
- Practice debugging with
gdb/strace. - See how tiny mistakes in C code = total pwnage.
- Builds a solid foundation for advanced wargames like Protostar or ROP Emporium.
By the end you’ll be comfortable with:
- Buffer overflows and memory corruption.
- Using
gdbto analyze stack/heap state. - Writing working exploits step by step.
- Thinking like a binary reverse engineer.
About This Series
Each level has its own post with:
- Login Info — how to connect for that level
- Task — the original OTW prompt
- Theory — notes on the bug type & C concepts
- Solution — step-by-step exploit until you get the next password
My goal isn’t to just dump payloads but to show why they work — so you can develop real binary exploitation skills.
How to Play Utumno (and actually learn)
- Read the source code carefully.
- Experiment with different inputs.
- Use
gdb,objdump,ltrace,straceto understand the binary. - Keep a notes file with offsets, registers, shellcode.
- Fail often, retry until the exploit works reliably.
Pro tip: never trust C functions like gets, strcpy, or unchecked buffers 😉
Levels Index (0 → 8)
Each link opens in a new tab. The one-liner tells you the main exploit idea for that level.
-
🐣 Level 0 — First Steps
Read post → — Warm-up challenge, simple buffer overflow. -
💻 Level 0 → 1 — Smashing the Stack
Read post → — Classic stack buffer overflow. -
🔥 Level 1 → 2 — Overwriting Variables
Read post → — Modify control flow via buffer overwrite. -
🎯 Level 2 → 3 — Function Pointers
Read post → — Exploit vulnerable function pointer usage. -
🧵 Level 3 → 4 — Off-by-One Fun
Read post → — Tiny off-by-one leads to control. -
🪓 Level 4 → 5 — Format String Attack
Read post → — Abuseprintfwith%n. -
📦 Level 5 → 6 — Return to Shellcode
Read post → — Inject and execute shellcode. -
🧩 Level 6 → 7 — Return-to-libc
Read post → — Bypass non-exec stack with libc. -
🏁 Level 7 → 8 — Final Boss
Read post → — Complex exploitation chain, end of Utumno 🎓
Conclusion
There are plenty of writeups out there, but this series is my own take — with my notes, thought process, and experiments. Hopefully it makes binary exploitation feel a bit less intimidating and a lot more fun.
Finishing Utumno feels like going from “overflow newbie” to “exploit padawan” ⚔️:
- You’ll see how small bugs lead to total compromise.
- Debuggers will become your best friends.
- You’ll be ready to tackle even harder games.
Next adventures:
- Narnia (intro exploitation)
- Behemoth (logic bugs & exploitation)
- Advanced labs: ROP Emporium / pwnable.kr
Keep pwning, keep debugging, keep notes — you got this 💪
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


