OverTheWire Natas Level 5 → 6 tutorial!!
Published on 18 Dec 2023
Login
URL: http://natas6.natas.labs.overthewire.org
Credentials: natas6:0RoJwHdSKWFTYR5WuiAewauSuNaBXned
Task
The page asks for a secret. If the secret is correct, it will reveal the password for natas7.
A little bit of Theory
- The page links to “View sourcecode”, which shows the PHP behind the challenge.
- PHP can include other files with
include/require. If the included file is web-accessible, you might read it directly. - Comparing
$_POST['secret']to a variable (like$secret) often means the real value sits in an included file.
Further reading:
Solution
-
Open the provided source
Click “View sourcecode” on the page.
<?php include "includes/secret.inc"; if (array_key_exists("submit", $_POST)) { if ($secret == $_POST['secret']) { print "Access granted. The password for natas7 is <censored>"; } else { print "Wrong secret"; } } ?>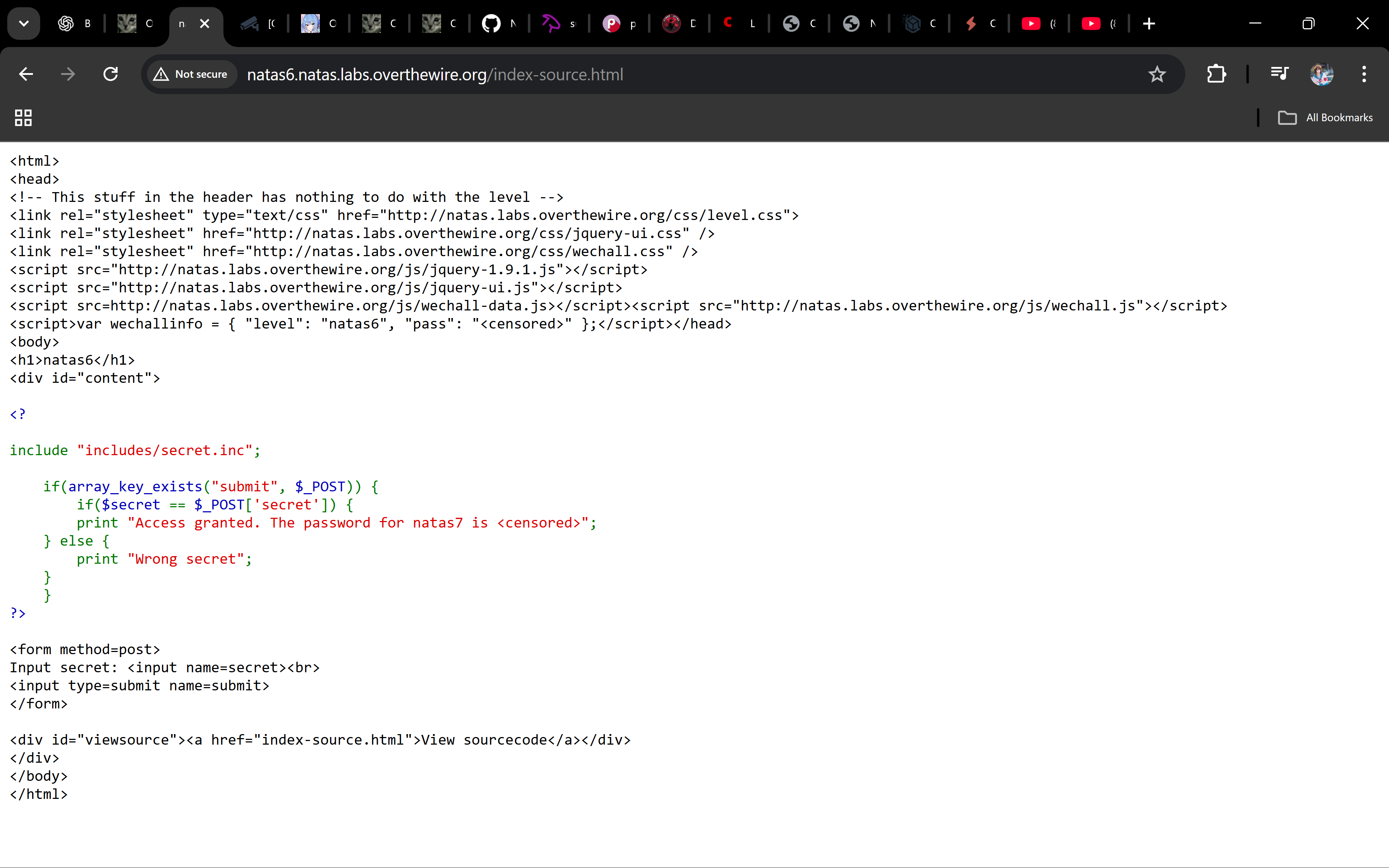
Why? It includes
includes/secret.inc, which likely defines$secret. -
Read the included file directly
Visit:
http://natas6.natas.labs.overthewire.org/includes/secret.incYou’ll see something like:
<?php $secret = "FOEIUWHGFEEUHFUOIVUOIU"; ?>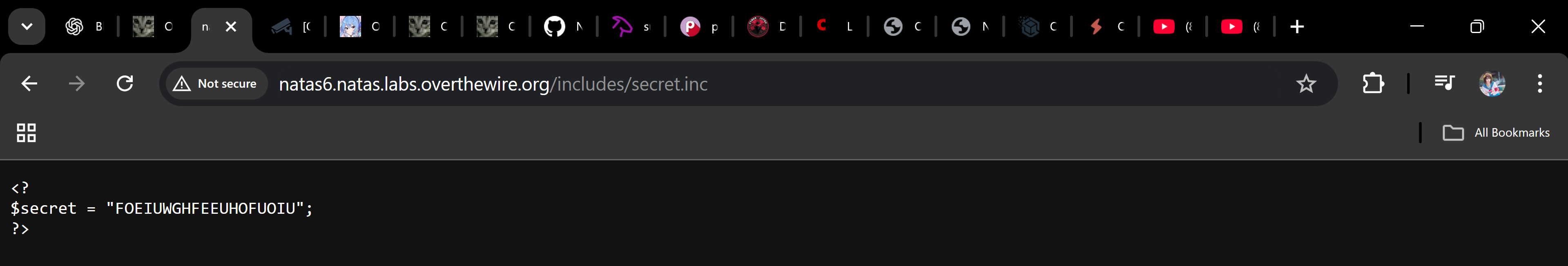
-
Submit the secret
Paste the secret into the form and press Submit.
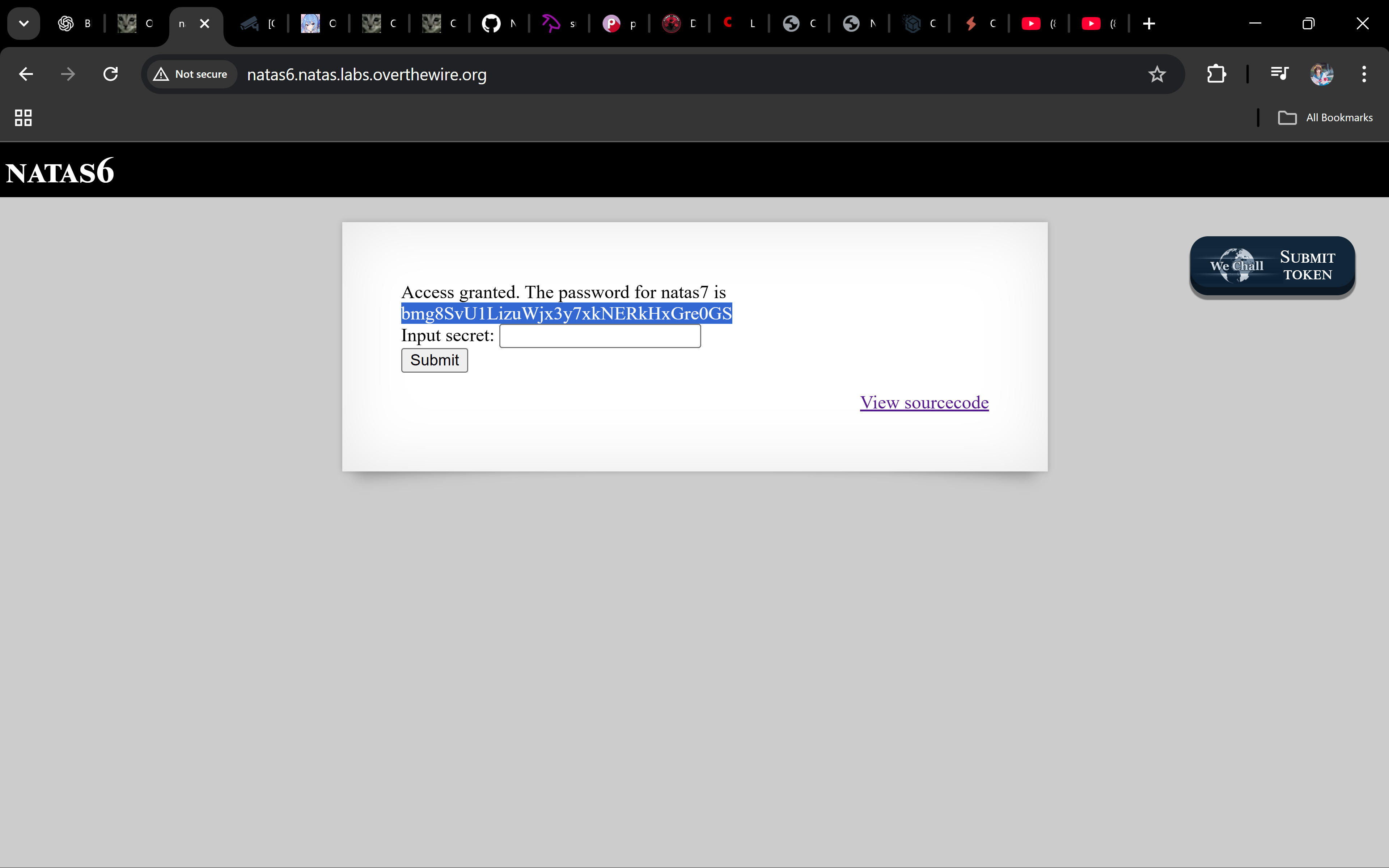
The page prints the password for natas7.
Password
bmg8SvU1LizuWjx3y7xkNERkHxGre0GS
Troubleshooting
- Getting “Wrong secret”? → Copy the secret exactly from
secret.inc(no spaces/newlines). - Can’t open
secret.inc? → Make sure the path is correct:/includes/secret.inc(case-sensitive). - Still stuck? → Re-check the Basic Auth credentials for natas6.
Great work 🎉 You traced an included file, grabbed the secret, and used it to unlock natas7!
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨

all tags
GOT-overwrite aboutme aead ai alphanumeric-shellcode apt argc0 argon2 aslr assembly asymmetric atoi automation backbox bandit base64 bash beginner behemoth binary binary-exploitation binary-to-ascii blackarch blind blind-sqli blogging blue-team bruteforce buffer-overflow buffer-overwrite c caesar canary capabilities checksec command-injection commonmark cookie cron crypto cryptography ctf cutter cyberchef cybersecurity defenders detection dev directory-traversal dnf docs drifter ecc education elf env envp exploitation finale forensics format-string formulaone frequency frequency-analysis gcc gdb getchar gfm ghidra github-pages governance gpg guide hashing hkdf http jekyll jmpbuf kali kasiski kdf kernel keylength kramdown krypton lab ld_preload leviathan lfi lfsr linux linux-syscall llmops log-poisoning ltrace manpage markdown maze memcpy mitigations mitmproxy mlops narnia natas networking newline-injection nonce nop-sled nx object-injection obsidian openssl osint overflow overthewire package-manager pacman parrot path path-hijacking pathname php pie pkc pki pointer-trick pqc priv-esc privilege-escalation provable-security pwn pwntools pyshark python race-condition radare2 rag randomness recon red-team redirect relro requests ret2env ret2libc reverse-engineering reversing ricing roadmap rop rot13 rsa scapy security seed seo serialization session setjmp-longjmp setuid shell shellcode smoke soc sockets sprintf sql-injection srop stack-canary stack-overflow strace strcmp strcpy streamcipher strings strncpy strtoul substitution suid suisei symlink symmetric terminal test threat-intel time-based tls troubleshooting tshark type-juggling ubuntu udp utumno vigenere virtualbox virtualization vmware vortex walkthrough web windows wireshark writing wsl x86

