OverTheWire Natas — Complete Walkthrough Index
OverTheWire Natas — Complete Walkthrough Index
Halloo SuiiKawaii dessu!! Glad to see you again. This page is the master index for my Natas walkthroughs — actually i don’t have much to say because the title and desciption already help you figure out what is this post about so yeah today we gonna do some OverTheWire Natas 🗣️🔥🔥🔥🔥!!

Introduction
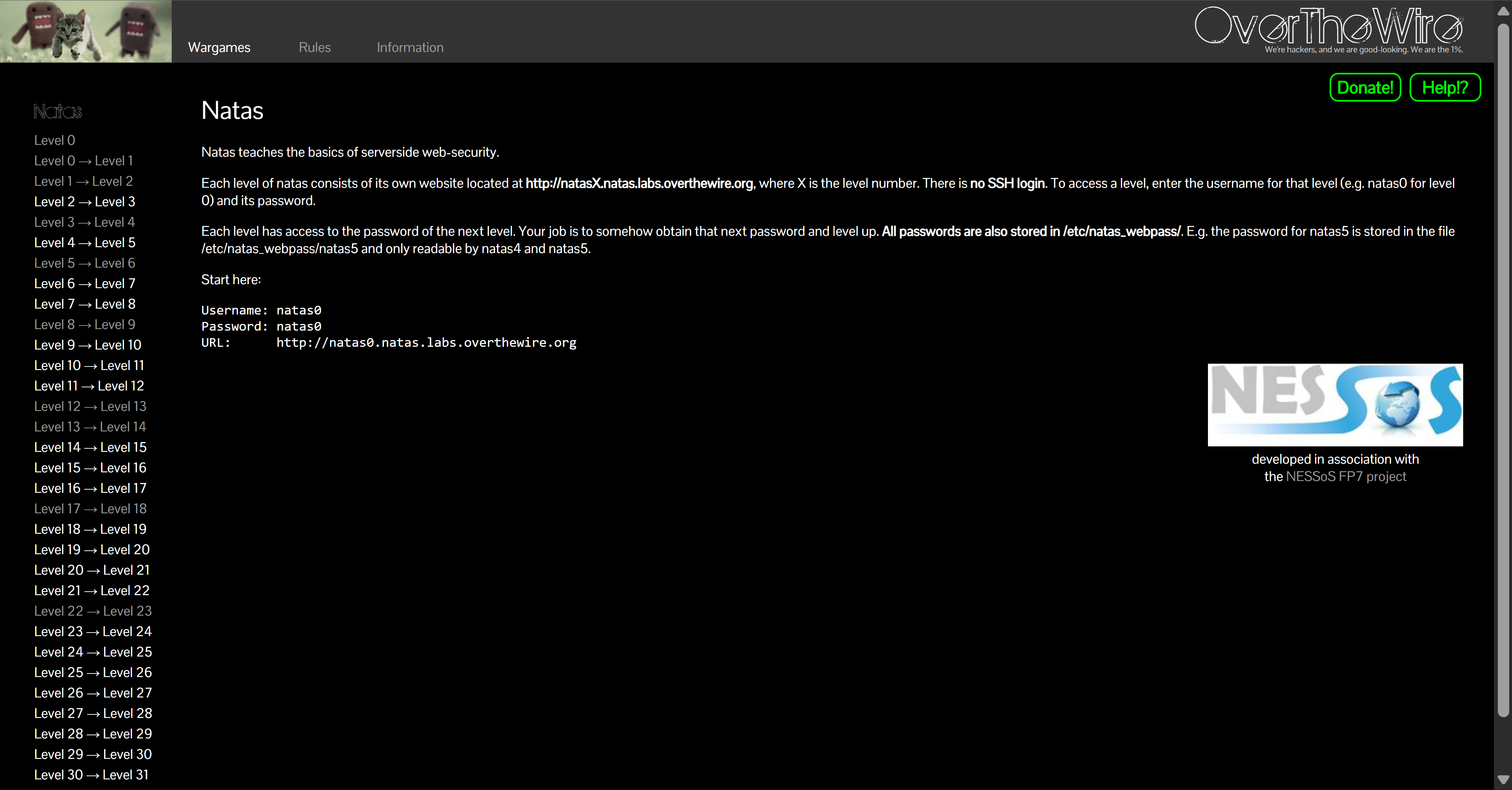
If you’re getting into cybersecurity or ethical hacking, OverTheWire (open in new tab) is one of the best beginner-friendly playgrounds for server-side web security. There’s no SSH — each level is a website at http://natasX.natas.labs.overthewire.org (X = level), logged in with the level’s username & password. :contentReference[oaicite:0]{index=0}
Natas currently spans Level 0 → Level 34. We’ll link every level below as posts go live. :contentReference[oaicite:1]{index=1}
Why play Natas?
- Hands-on web vulns from the ground up.
- Builds instincts with headers, cookies, auth, encoding.
- Touches LFI/RFI, SQLi, XSS, CSRF, uploads, regex filters, and more.
- Totally free — just a browser + network tools.
By the end you’ll be comfortable with:
- Reading/altering HTTP requests (
curl, Burp, devtools). - Inspecting source, responses, headers, cookies, sessions.
- Turning small observations into repeatable exploits.
About This Series
Each level has its own post with:
- Login Info — how to connect for that level
- Task — the original OTW prompt
- Theory — short notes on the concepts
- Solution — step-by-step, reproducible walkthrough
My goal isn’t to dump passwords but to show why each step works so you can solve similar problems on your own.
How to Play Natas (and actually learn)
- Read the page + source carefully.
- Try first, then peek at hints if stuck.
- Use devtools/Burp/
curlaggressively. - Keep a logbook of requests, payloads, dead ends.
- Fail fast, retry until you can solve it without notes.
Pro tip: tiny, repeatable HTTP requests beat guesswork — save them and iterate.
Levels Index (0 → 34)
Each link opens in a new tab. The one-liner tells you the main idea for that level.
-
🐣 Level 0 — View Source Basics
Read post → — Inspect HTML to find the next password. -
🧰 Level 0 → 1 — DevTools > Right-click
Read post → — Bypass UI tricks; use keyboard/devtools. -
🧭 Level 1 → 2 — Follow the Hints
Read post → — Comments/paths lead to the secret. -
🤖 Level 2 → 3 — robots.txt / Directory Listing
Read post → — Crawl what you’re not “supposed” to. -
🗂️ Level 3 → 4 — Hidden Files
Read post → — Explore subdirs and ignore lists. -
📨 Level 4 → 5 — HTTP Headers
Read post → — TweakReferer/User-Agentstyle checks. -
🍪 Level 5 → 6 — Cookies Matter
Read post → — Decode/flip cookie state. -
🔁 Level 6 → 7 — Include & Traversal
Read post → — LFI/RFI-like behavior and filters. -
🧮 Level 7 → 8 — Grep/Keyword Gate
Read post → — Server-side search quirks. -
🪄 Level 8 → 9 — Encoding Tricks
Read post → — Base64/URL/hex layers; order matters. -
🧩 Level 9 → 10 — Regex Filters
Read post → — Bypass naive server-side regex. -
🧪 Level 10 → 11 — Blacklist Evasion
Read post → — Payload shaping vs filter rules. -
🧑🍳 Level 11 → 12 — Cookie Crafting
Read post → — Sign/encode/flip until admin. -
🔐 Level 12 → 13 — File Upload (I)
Read post → — Content-type/extension checks. -
🧰 Level 13 → 14 — File Upload (II)
Read post → — Double-ext/MIME & execution path. -
🕳️ Level 14 → 15 — SQLi (Boolean/Time)
Read post → — Extract via blind techniques. -
🧠 Level 15 → 16 — Timing & Truth Tables
Read post → — Automate blind checks. -
🧯 Level 16 → 17 — Command Injection
Read post → — Escape shells/filters, capture output. -
🗃️ Level 17 → 18 — Session/Temp Files
Read post → — Enumerate session storage. -
🧵 Level 18 → 19 — Race Conditions
Read post → — TOCTOU-style tricks. -
🧷 Level 19 → 20 — Password Handling
Read post → — Hashing/verification quirks. -
🧮 Level 20 → 21 — PRNG/Token Logic
Read post → — Predict or abuse weak randomness. -
📨 Level 21 → 22 — Email/Exec Chain
Read post → — Injection via mail/handler. -
🧩 Level 22 → 23 — Auth Bypass
Read post → — Think outside the form. -
🗜️ Level 23 → 24 — Serialization
Read post → —unserialize-style gadget fun. -
🧪 Level 24 → 25 — Password-Reset Flow
Read post → — Token/account logic flaws. -
🧠 Level 25 → 26 — CSP/XSS Games
Read post → — Script sinks and exfil. -
🧲 Level 26 → 27 — Filter Gymnastics
Read post → — Encode/concatenate to bypass. -
🧵 Level 27 → 28 — Crypto/Encoding Mix
Read post → — Layered transforms. -
🪄 Level 28 → 29 — Magic Values
Read post → — Signatures & type juggling. -
🧰 Level 29 → 30 — Git/Config Artifacts
Read post → — Repo/history leaks. -
🔁 Level 30 → 31 — Service Misuse
Read post → — Chain external helpers. -
🧪 Level 31 → 32 — Sandbox Escape
Read post → — Restricted exec evasion. -
🧠 Level 32 → 33 — Logic Puzzle
Read post → — Combine previous skills. -
🏁 Level 33 → 34 — Final!
Read post → — Wrap-up challenge 🎓
Conclusion
There are tons of guides out there from other Blog to Youtube videos, but i made this series is my take with my own style of workflow, notes, and explanations. Even if you just skim, I hope it will helps you learn faster.
Finishing Natas feels like leveling up from “web noob” to request-slinging ninja 🥷:
- HTTP becomes a friendly toolbox.
- You can chain small tricks into real exploits.
- You can learn anything by slicing it into tiny, winnable steps.
Next adventures:
- Krypton (crypto)
- Narnia (binary exploitation)
- Labs: TryHackMe / Hack The Box
Keep playing, keep breaking (legally!), keep notes — you got this 💪
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


