OverTheWire Manpage — Complete Walkthrough Index
OverTheWire Manpage — Complete Walkthrough Index
Halloo SuiiKawaii dessu!! Glad to see you again. This page is the master index for my Manpage walkthroughs — actually i don’t have much to say because the title and desciption already help you figure out what is this post about so yeah today we gonna do some OverTheWire Manpage 🗣️🔥🔥🔥🔥!!

Introduction
If you’re getting into cybersecurity or ethical hacking, OverTheWire (open in new tab) is one of the best beginner-friendly playgrounds.
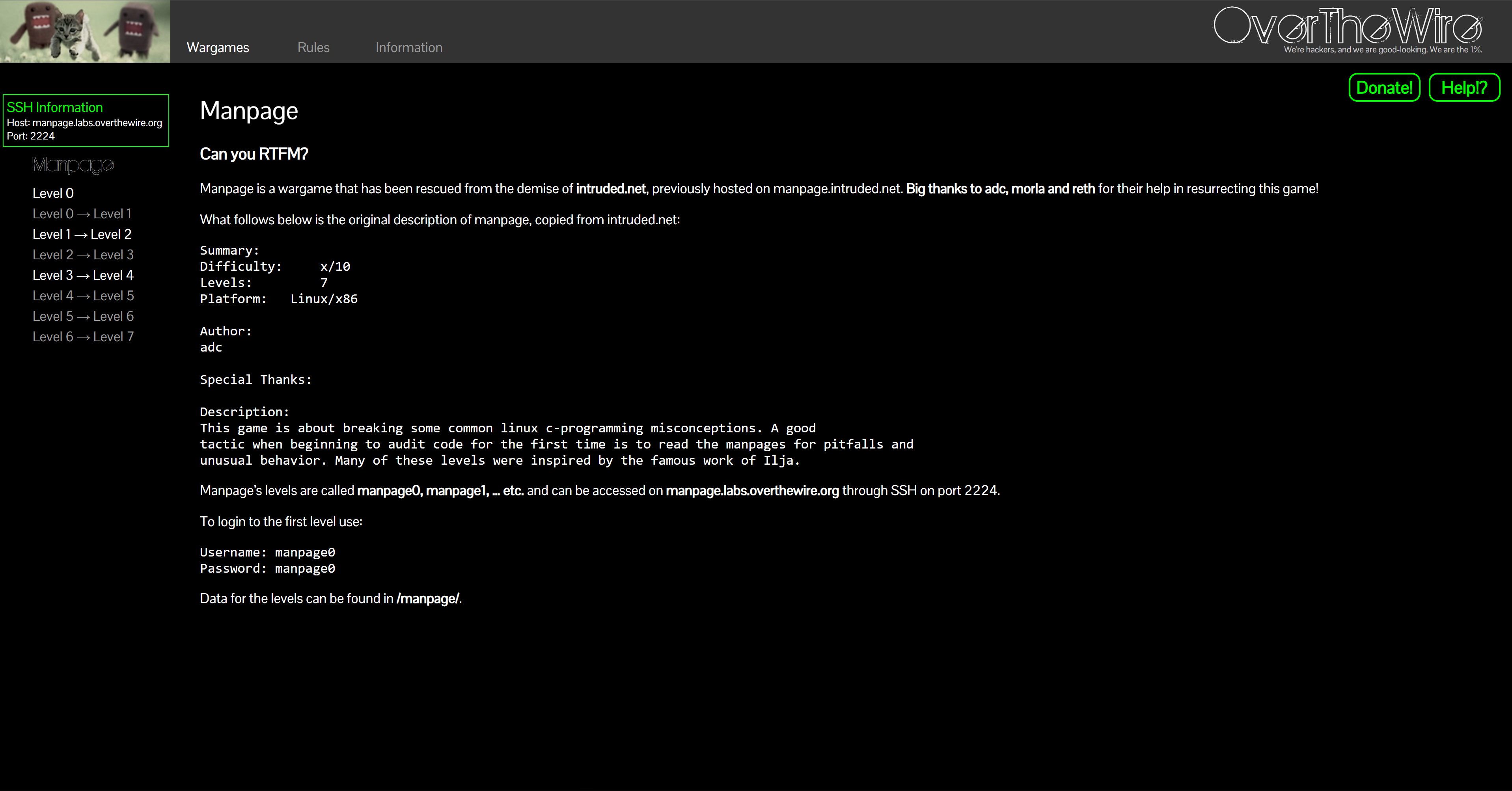
Manpage is a compact wargame that trains you to RTFM like a pro — digging through manual pages, understanding flags/sections, and spotting “gotchas” hidden in docs. It’s perfect for sharpening real-life troubleshooting and research skills you’ll reuse in CTFs and pentesting.
Why play Manpage?
- Hands-on doc-reading under pressure.
- Builds research discipline: find, verify, reproduce.
- Teaches “read the fine manual” habits that save hours.
- Totally free — just a terminal + internet.
By the end you’ll be comfortable with:
- Navigating
maneffectively: sections,/search, jumps. - Using
man -k/aproposto discover the right tool. - Reading NOTES / CAVEATS to avoid classic pitfalls.
About This Series
Each level has its own post with:
- Login Info — how to connect for that level
- Task — the original OTW prompt
- Theory — short notes on the commands/concepts
- Solution — step-by-step, reproducible walkthrough
My goal isn’t to dump passwords but to show why each step works so you can solve similar problems on your own.
How to Play Manpage (and actually learn)
- Read the challenge carefully.
- Try first, then peek at hints if stuck.
- Use
man/--helpaggressively. - Keep a logbook of commands, ideas, dead ends.
- Fail fast, retry until you can solve it without notes.
Pro tip: master man -k, sections (e.g., man 2 open), and in-page search with /keyword + n.
Levels Index (0 → 7)
Each link opens in a new tab. The one-liner tells you the main idea for that level.
-
🐣 Level 0 — SSH Login & Layout
Read post → — SSH in & see where things live. -
📖 Level 0 → 1 — Manpage Basics
Read post → — Open pages, navigate,/search. -
🔎 Level 1 → 2 —
man -k/apropos
Read post → — Find the right page by keyword. -
🧭 Level 2 → 3 — Sections (1–8)
Read post → — Choose the correct section (e.g.,man 2vsman 3). -
⚙️ Level 3 → 4 — Options, ENV, Exit Codes
Read post → — Read flags & behavior precisely. -
📝 Level 4 → 5 — NOTES & CAVEATS
Read post → — Catch the quirks hidden in docs. -
🧩 Level 5 → 6 — Stitching Commands
Read post → — Combine tools per spec. -
🏁 Level 6 → 7 — Final Checks
Read post → — Validate assumptions & edge cases.
Conclusion
There are tons of guides out there from other Blog to Youtube videos, but i made this series is my take with my own style of workflow, notes, and explanations. Even if you just skim, I hope it will helps you learn faster.
Finishing Manpage feels like leveling up your research superpower 🧠:
- Manuals become your best friend.
- You can extract answers quickly from dense docs.
- You can learn anything by slicing it into tiny, winnable steps.
Next adventures:
- Krypton (crypto)
- Narnia (binary exploitation)
- Labs: TryHackMe / Hack The Box
Keep playing, keep breaking (legally!), keep notes — you got this 💪
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


