OverTheWire Behemoth Level 0 tutorial!!
Login
For Behemoth, the server details are:
ssh behemoth0@behemoth.labs.overthewire.org -p 2221
# password: behemoth0
Username: behemoth0
Host: behemoth.labs.overthewire.org
Port: 2221
Password: behemoth0
Task
Level 0 is the warm-up. The only challenge is to log into the server successfully. From here, you’ll move on to interacting with real setuid binaries.
A little bit of Theory
-
SSH (Secure Shell) is used to connect securely to a remote machine.
-
General syntax:
ssh <username>@<host> -p <port> -
Here:
behemoth0= usernamebehemoth.labs.overthewire.org= host-p 2221= custom port for Behemoth
Once logged in, you start in /home/behemoth0. Every new level will escalate into a different user account (behemoth1, behemoth2, …) once you solve the binary.
Further reading:
Solution
-
Open a terminal Works on macOS/Linux. On Windows, use PowerShell/WSL/PuTTY.
-
Run the SSH command:
ssh behemoth0@behemoth.labs.overthewire.org -p 2221→ This starts a secure session as user behemoth0.
-
First-time connection: You’ll be asked to trust the host key. Type
yes. -
Enter the password:
behemoth0(Note: input is hidden for security, just type it in.)
-
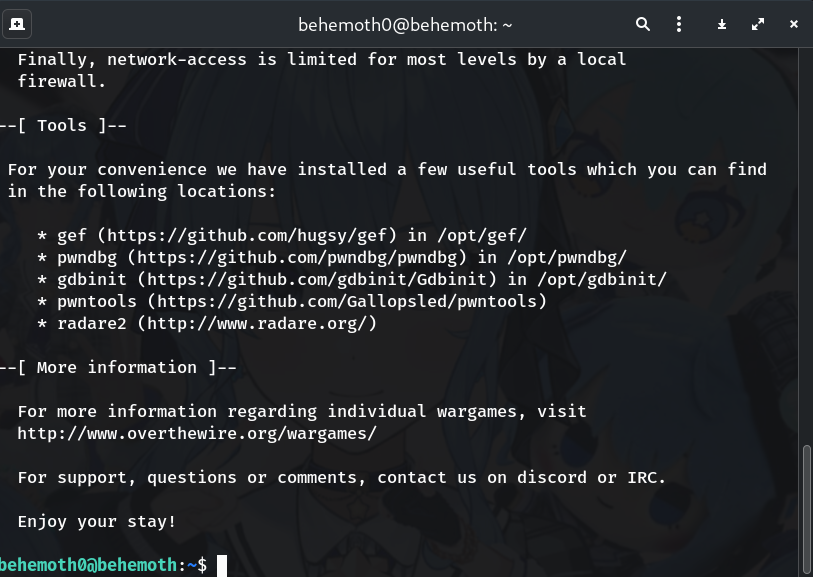
Verify login: You should see something like:
behemoth0@behemoth:~$Confirm with:
whoami # should print: behemoth0 pwd # should print: /home/behemoth0 -
Disconnect when done:
exit
Troubleshooting Quick Tips
ssh: connect to host ... port 2221: Connection timed out→ Check firewall/internet.Permission denied→ Double-check username (behemoth0) and password (behemoth0).Host key verification failed→ Remove the old entry in~/.ssh/known_hosts.
Congrats 🎉 You’ve successfully logged into Behemoth Level 0. Next, we’ll start playing with actual binaries 👾
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


