OverTheWire Bandit Level 9 → 10 tutorial!!
Login
Log in as bandit9 using the password you just obtained from Level 8 → 9.
ssh bandit9@bandit.labs.overthewire.org -p 2220
# password: 4CKMh1JI91bUIZZPXDqGanal4xvAg0JM
Why? Each Bandit level is a separate UNIX user. To solve 9 → 10, you must be the
bandit9user.
Task
The password for the next level is stored in data.txt and appears as a human-readable string preceded by several = characters.
A little bit of Theory
-
stringsextracts printable (ASCII) sequences from a (possibly) binary file.- Minimum length:
-n 4(often default). - Show offsets (optional):
-t x(hex) or-t d(decimal).
- Minimum length:
-
grepfilters lines by pattern.- Regex for three-or-more equals signs:
-E '={3,}'
- Regex for three-or-more equals signs:
-
Pipe
strings→grepto cut noise fast.
Further reading:
Solution
-
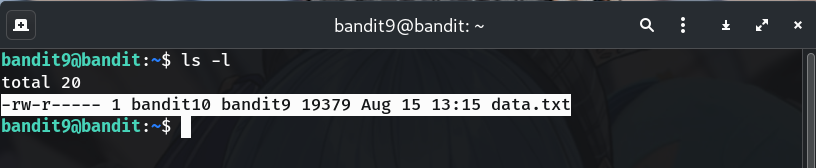
Confirm the file is present
ls -lWhy? Sanity check that
data.txtexists and you’re in the right place.
-
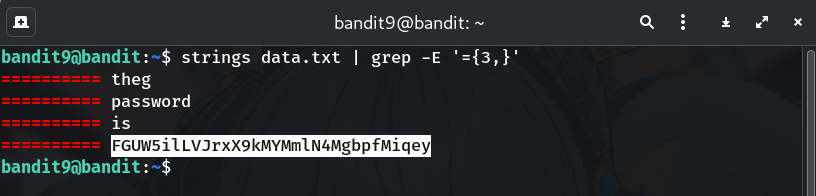
Extract printable strings and look for
===strings data.txt | grep -E '={3,}' # or, slightly stricter to capture the token after the equals: strings data.txt | grep -E '={3,}[A-Za-z0-9+/=]{8,}'Why?
stringssurfaces human-readable chunks;grepnarrows to the few lines preceded by equals signs.
-
(Optional) Show offsets
strings -t x data.txt | grep -E '={3,}'Why? Offsets help you verify where the readable text sits inside the file (not required to solve).
-
Copy the password (no extra spaces/newlines).
-
Log into the next level (bandit10)
exit ssh bandit10@bandit.labs.overthewire.org -p 2220 # paste the password you just found when prompted
Password
This is the password shown in my run; if yours differs, copy the one from your own terminal output.
FGUW5ilLVJrxX9kMYMmlN4MgbpfMiqey
Troubleshooting
- Too much output from
strings? → Add the filter:grep -E '={3,}'. - Still nothing? → Try the looser
grep '==='(regex flavors differ slightly). - Odd characters? → Force C locale:
LC_ALL=C strings data.txt | grep '==='.
Congrats 🎉 You carved the hidden text out of a binary and can now play as bandit10.
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


