OverTheWire Bandit Level 7 → 8 tutorial!!
Login
Log in as bandit7 using the password you just obtained from Level 6 → 7.
ssh bandit7@bandit.labs.overthewire.org -p 2220
# password: morbNTDkSW6jIlUc0ymOdMaLnOlFVAaj
Why? Each Bandit level is a separate UNIX user. To solve 7 → 8, you must be the
bandit7user.
Task
The password for the next level is stored in the file data.txt and is on the same line as the word millionth.
A little bit of Theory
-
grepsearches for lines that match a pattern.- Basic:
grep PATTERN FILE - With line numbers:
grep -n PATTERN FILE - Match a whole word:
grep -w PATTERN FILE
- Basic:
-
The output line typically looks like:
millionth <password>→ copy the second field. You can also extract it withawkorcut.
Further reading:
Solution
-
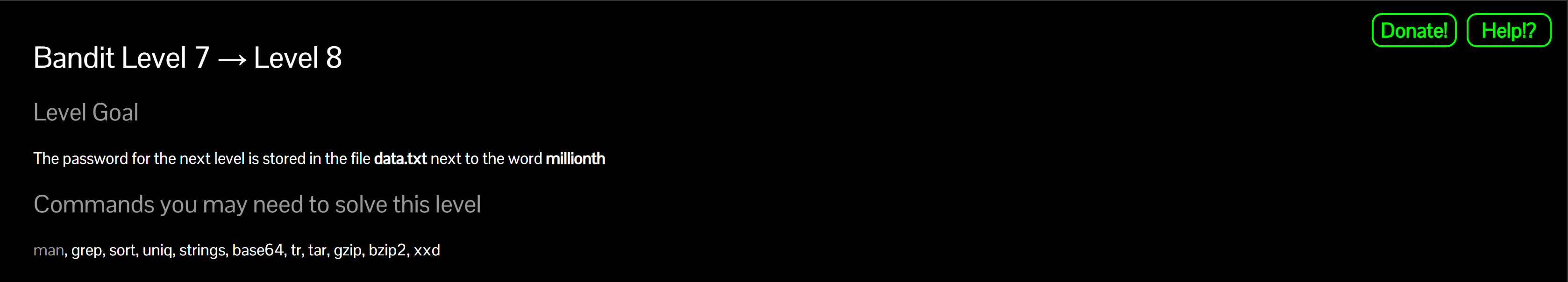
Verify the file is present
ls -lWhy? Sanity check; the challenge states
data.txtis here.
-
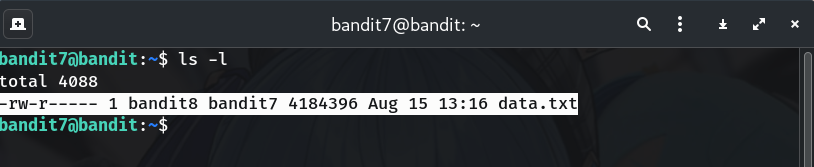
Search for the keyword
grep -nw 'millionth' data.txtWhy?
-nshows the line number;-wforces a whole-word match. -
(Optional) Extract only the password
awk '/\bmillionth\b/ {print $2}' data.txt # or: grep -w 'millionth' data.txt | cut -d' ' -f2Why? Prints just the second field (the password) — copy-friendly.
-
Copy the password (no extra spaces/newlines).
-
Log into the next level (bandit8)
exit ssh bandit8@bandit.labs.overthewire.org -p 2220 # paste the password you just found when prompted
Password
This is the password shown in my run; if yours differs, copy the one from your own terminal output.
dfwvzFQi4mU0wfNbFOe9RoWskMLg7eEc
Troubleshooting
grep: data.txt: No such file or directory→ Checkpwd; you should be in/home/bandit7.- Multiple matches? → Use
-wto match the whole word. - Output formatting odd? → Use
awk/cutas shown to isolate the second field.
Congrats 🎉 You plucked the right line out of a huge file and can now play as bandit8.
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


