OverTheWire Bandit Level 6 → 7 tutorial!!
Login
Log in as bandit6 using the password you just obtained from Level 5 → 6.
ssh bandit6@bandit.labs.overthewire.org -p 2220
# password: HWasnPhtq9AVKe0dmk45nxy20cvUa6EG
Why? Each Bandit level is a separate UNIX user. To solve 6 → 7, you must be the
bandit6user.
Task
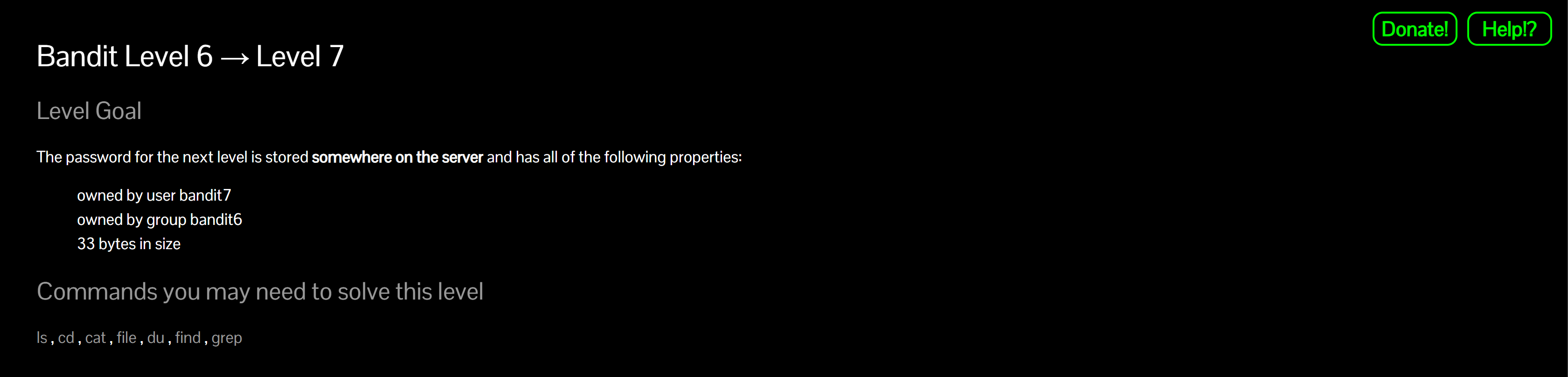
The password for the next level is stored somewhere on the server and the file has all of these properties:
- owned by user
bandit7 - owned by group
bandit6 - 33 bytes in size
A little bit of Theory
-
Use
findto search from the filesystem root/with multiple predicates:- Owner:
-user bandit7 - Group:
-group bandit6 - Size:
-size 33c(thecmeans bytes) - Regular file (defensive):
-type f
- Owner:
-
Searching from
/will hit many restricted dirs and print errors. Suppress those stderr messages with:2>/dev/null -
Full example:
find / -type f -user bandit7 -group bandit6 -size 33c 2>/dev/null -
After you get the path,
cat <path>to reveal the password.
Further reading:
Solution
-
Run
findfrom the root with all constraintsfind / -type f -user bandit7 -group bandit6 -size 33c 2>/dev/nullWhy? Walks the whole filesystem, returning only regular files that match the exact owner, group, and size.
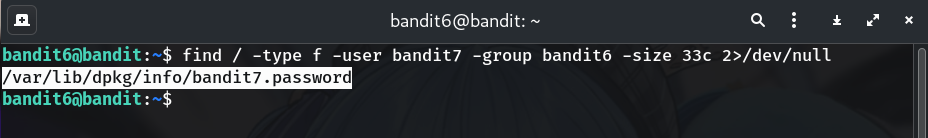
Example output (from my run):
/var/lib/dpkg/info/bandit7.password
-
Print the password
cat /var/lib/dpkg/info/bandit7.password # use the actual path you found in Step 1Why? The matching file contains the next level’s password.
-
Copy the password (no extra spaces/newlines).
-
Log into the next level (bandit7)
exit ssh bandit7@bandit.labs.overthewire.org -p 2220 # paste the password you just found when prompted
Password
This is the password shown in my run; if yours differs, copy the one from your own terminal output.
morbNTDkSW6jIlUc0ymOdMaLnOlFVAaj
Troubleshooting
- Tons of “Permission denied”? → Keep
2>/dev/nullto silence stderr; the valid result will still print. - No result? → Double-check predicates (
-user bandit7 -group bandit6 -size 33c -type f) and ensure thecsuffix is present. - Multiple hits? → Very unlikely; if it happens,
ls -l <path>to confirm owner/group/size = 33 bytes.
Congrats 🎉 You hunted across the filesystem and can now play as bandit7.
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


