OverTheWire Bandit Level 4 → 5 tutorial!!
Login
Log in as bandit4 using the password you just obtained from Level 3 → 4.
ssh bandit4@bandit.labs.overthewire.org -p 2220
# password: 2WmrDFRmJIq3IPxneAaMGhap0pFhF3NJ
Why? Each Bandit level is a different UNIX user; to solve 4 → 5 you must be
bandit4.
Task
The password for the next level is stored in the only human-readable file inside the directory inhere in bandit4’s home.
A little bit of Theory
- The directory currently contains files named
-file00…-file09(note the leading-). -
Many commands treat a leading
-as an option. Safest is to prefix with./or use--:file ./* # OK: expands to ./-file00, ./-file01, ... cat ./-file07 # OK cat -- -file07 # also OK -
Use
fileto identify which entry is ASCII text (human-readable). To avoid false positives, filter exactly: ASCII text(not “Non-ISO extended-ASCII”):file ./* | grep ': ASCII text' - Then
catthat filename to print the password.
Further reading (open in new tab):
Solution (step-by-step, with reasons)
-
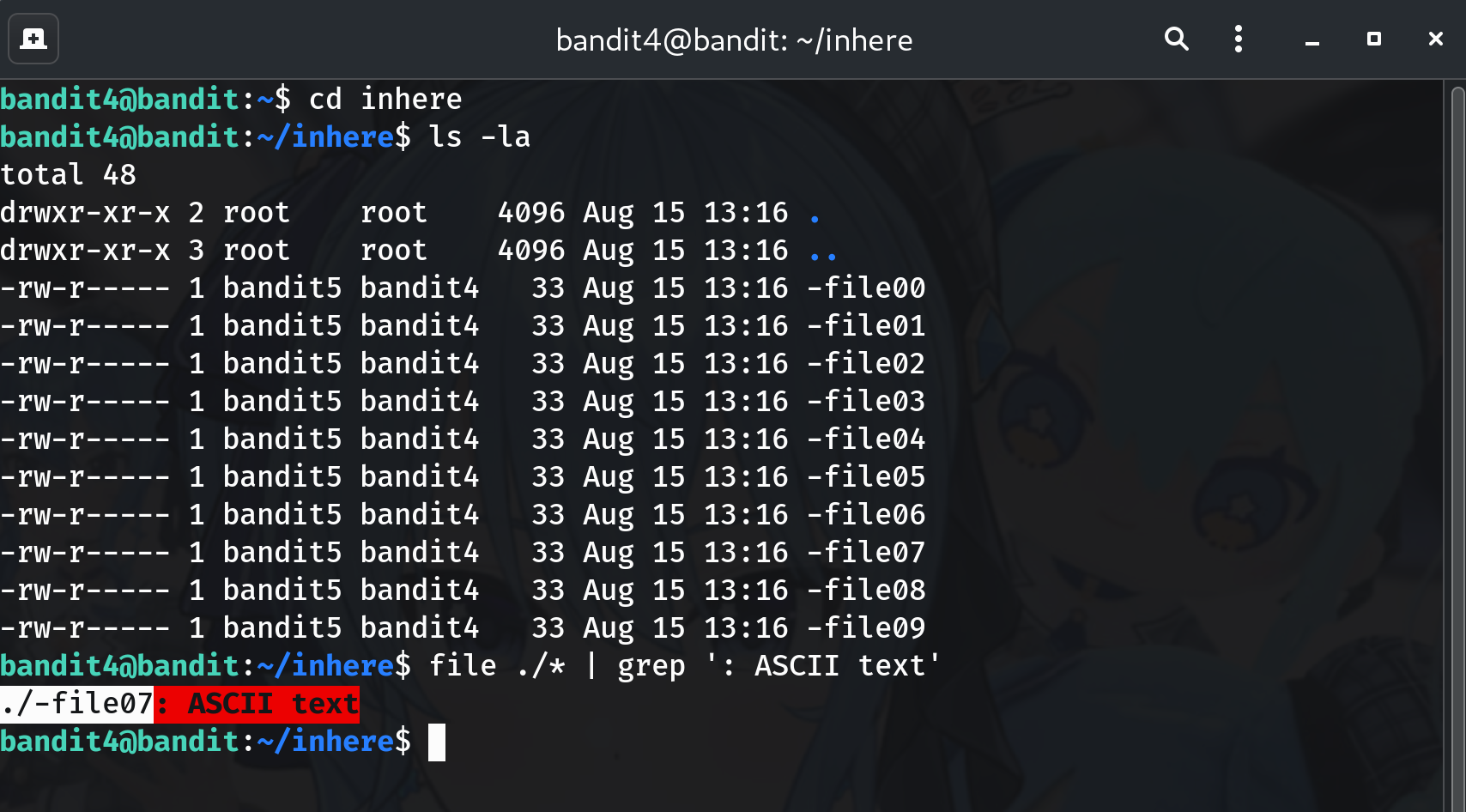
Move into the directory with the files
cd inhereWhy? The challenge says all candidate files are here.
-
Identify the only human-readable file
file ./* | grep ': ASCII text'Why?
fileclassifies each entry; the grep narrows to the single ASCII text file.
-
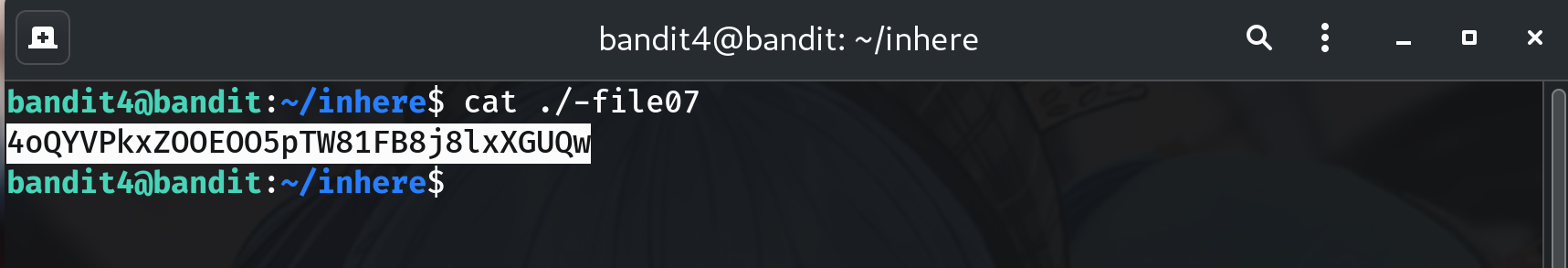
Print the password Suppose the previous command showed
./-file07: ASCII text. Read it with:cat ./-file07 # or: cat -- -file07Why? Prefixing with
./(or using--) prevents the leading dash from being parsed as an option.
-
Copy the password (no extra spaces/newlines).
-
Log into the next level (bandit5)
exit ssh bandit5@bandit.labs.overthewire.org -p 2220 # paste the password you just found when prompted
Password
This is the password shown in my run; if yours differs, copy the one from your own terminal output.
4oQYVPkxZOOEOO5pTW81FB8j8lxXGUQw
Troubleshooting
cat: invalid option→ Usecat ./-filenameorcat -- -filename.No such file or directory→ Ensure youcd inhereand copy the filename exactly.- Terminal looks weird after
cat→ You probably viewed a binary; runreset, then usefile ./* | grep ': ASCII text'.
Congrats 🎉 You found the only human-readable file and can now play as bandit5.
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


