OverTheWire Bandit Level 30 → 31 tutorial!!
Login
Log in as bandit30 using the password you obtained from Level 29 → 30.
ssh bandit30@bandit.labs.overthewire.org -p 2220
# password: qp30ex3VLz5MDG1n91YowTv4Q8l7CDZL
Why? Each Bandit level is a separate UNIX user. To solve 30 → 31, you must be the
bandit30user.
Task
There is a git repository at
ssh://bandit30-git@localhost:2220/home/bandit30-git/repo
The password for bandit30-git is the same as for bandit30.
Clone the repo and find the password for bandit31.
A little bit of Theory
- Git doesn’t only track commits/branches; it also has tags (often used for releases).
- Annotated tags store a message (and metadata). Bandit hides secrets inside the tag message.
-
Commands you’ll need:
git tag -l— list tagsgit show <tag>— display what a tag points to (and the message)- (alt)
git cat-file -p <tag>— print raw tag object
Further reading:
Solution
-
Clone the repository into a writable temp dir
WORKDIR=$(mktemp -d) cd "$WORKDIR" git clone ssh://bandit30-git@localhost:2220/home/bandit30-git/repo "repo-$RANDOM" cd repo-*Why?
/tmpis writable. When prompted forbandit30-git@localhost’s password, use your bandit30 password.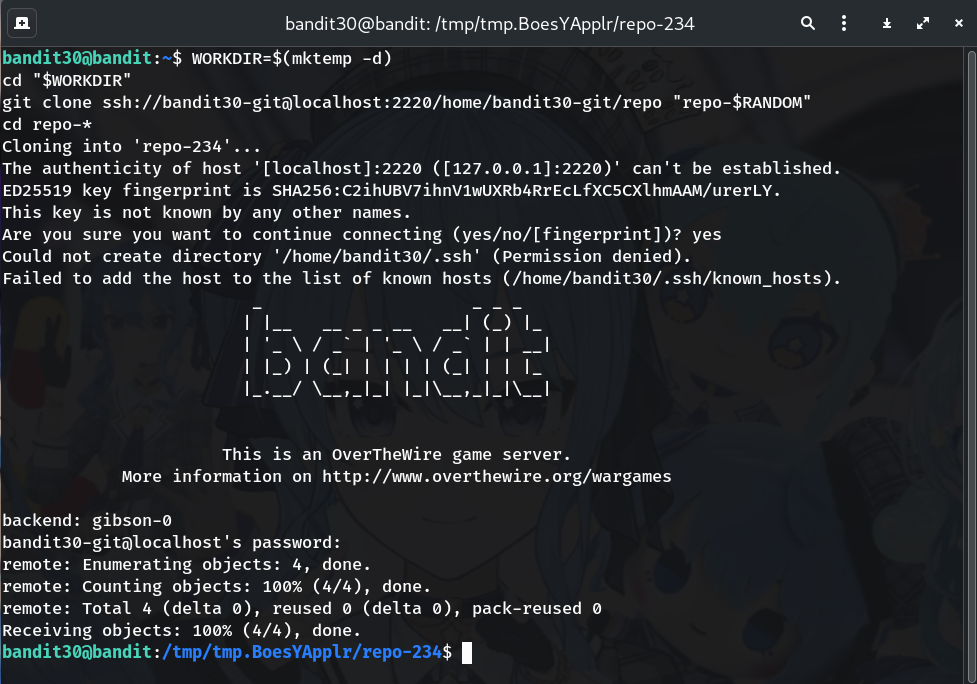
-
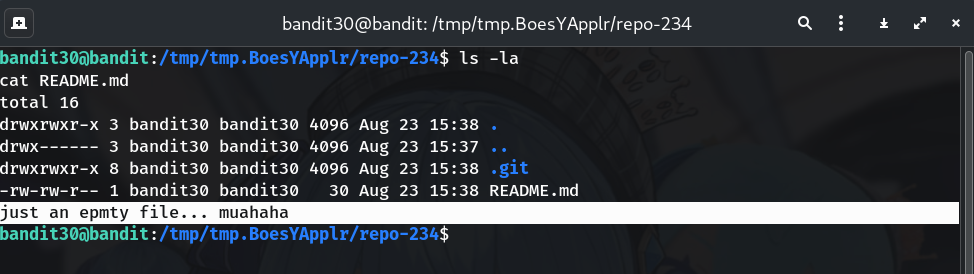
Quick look at the repo
ls -la cat README.mdWhy? Often the working tree looks clean; the hint is that the secret isn’t in files but elsewhere (tags).
-
List tags
git tag -lYou should see something like:
secretWhy? Tags are another place to stash data; here the tag name is a dead giveaway.
-
Show the tag’s contents
git show secret # alt: git cat-file -p secretThe annotated tag message prints the password for bandit31.
Why?
git showrenders the tag message; Bandit places the password right there.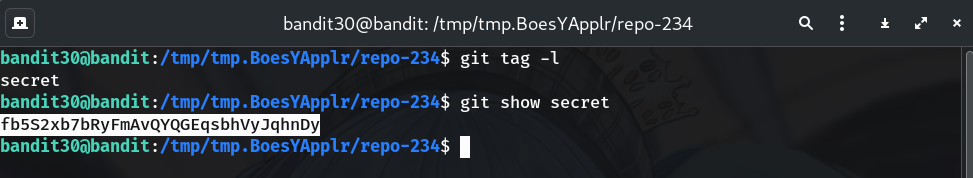
Password
This is the password revealed by the tag in my run (use the one your terminal prints):
fb5S2xb7bRyFmAvQYQGEqsbhVyJqhnDy
Troubleshooting
- “unknown revision or path not in the working tree” → Make sure you’re inside the cloned repo folder (
cd repo-*) and that the tag exists (git tag -l). - Tag name differs → List with
git tag -nand show the one you see, or rungit show refs/tags/<name>. - Auth issues cloning → Use the exact URL and port:
ssh://bandit30-git@localhost:2220/...and enter your bandit30 password when prompted.
Congrats 🎉 You used git tags to uncover a hidden secret. On to bandit31!
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


