OverTheWire Bandit Level 2 → 3 tutorial!!
Login
Log in as bandit2 using the password you just obtained from Level 1 → 2.
ssh bandit2@bandit.labs.overthewire.org -p 2220
# password: 263JGJPfgU6LtdEvgfWU1XP5yac29mFx
Why? Each Bandit level is a separate UNIX user. To solve 2 → 3, you must be the
bandit2user.
Task
The password for the next level is stored in a file named –spaces in this filename– located in the home directory of bandit2.
A little bit of Theory
- Filenames with spaces must be quoted or escaped so the shell treats them as a single argument.
-
Filenames beginning with
-can be interpreted as options. Safe ways to reference them:-
Prefix with a path:
cat "./--spaces in this filename--" -
Use the option terminator:
cat -- "--spaces in this filename--" -
Escape spaces (and still add
./so the leading dashes aren’t parsed as options):cat ./--spaces\ in\ this\ filename--
-
- Tab completion helps avoid typos: type
cat ./--spa<Tab>and let the shell complete the filename. ls -lashows file details to confirm you’re in the right place.
Further reading:
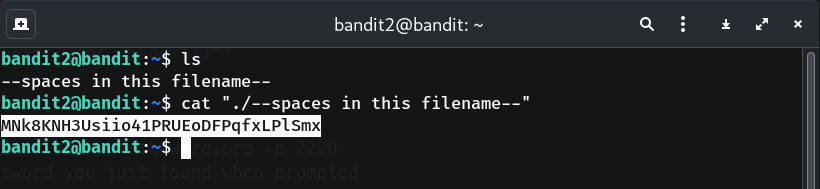
Solution
-
Confirm your location
pwdWhy? Should print
/home/bandit2; that’s where the target file lives. -
List files to see the target
ls -laWhy? Verifies the file –spaces in this filename– exists and shows its permissions.
-
Read the file safely
cat "./--spaces in this filename--" # or cat -- "--spaces in this filename--" # or cat ./--spaces\ in\ this\ filename--Why? Quoting/escaping and/or prefixing with a path prevents the leading dashes from being treated as options.
-
Copy the password (no extra spaces/newlines).
-
Log into the next level (bandit3)
exit ssh bandit3@bandit.labs.overthewire.org -p 2220 # paste the password you just found when prompted
Password
This is the password shown in my run; if yours differs, copy the one from your own terminal output.
MNk8KNH3Usiio41PRUEoDFPqfxLPlSmx
Troubleshooting
No such file or directory→ Include the leading/trailing--and quote/escape spaces; try Tab completion.cat: invalid option→ Usecat -- "--filename"or add./before the name.Permission denied→ Ensure you are logged in asbandit2.
Congrats 🎉 You handled filenames with spaces and can now play as bandit3.
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


