OverTheWire Bandit Level 11 → 12 tutorial!!
Login
Log in as bandit11 using the password you just obtained from Level 10 → 11.
ssh bandit11@bandit.labs.overthewire.org -p 2220
# password: dtR173fZKb0RRsDFSGsg2RWnpNVj3qRr
Why? Each Bandit level is a separate UNIX user. To solve 11 → 12, you must be the
bandit11user.
Task
The password for the next level is stored in data.txt, where all letters (a–z, A–Z) have been rotated by 13 positions (ROT13).
A little bit of Theory
- ROT13 is a simple substitution cipher that rotates letters by 13 places. Applying ROT13 twice returns the original text.
-
Decode ROT13 with
tr:tr 'A-Za-z' 'N-ZA-Mn-za-m'The first character set is mapped to the second one, performing the rotation.
-
Combine with pipes to transform file contents:
cat data.txt | tr 'A-Za-z' 'N-ZA-Mn-za-m'
Further reading:
Solution
-
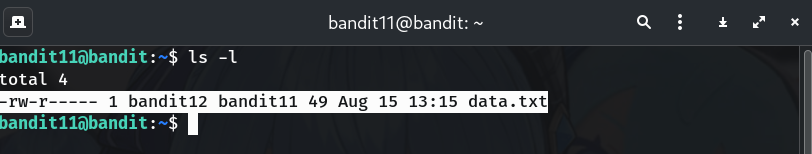
Check the file is present
ls -lWhy? Confirms
data.txtexists and you’re in the right directory.
-
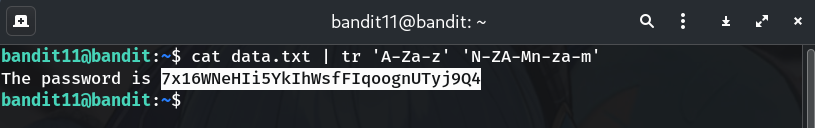
Decode with
trcat data.txt | tr 'A-Za-z' 'N-ZA-Mn-za-m'Why? Maps each letter to the one 13 places away, revealing the plaintext containing the password.
-
Copy the password (no trailing spaces/newlines).
-
Log into the next level (bandit12)
exit ssh bandit12@bandit.labs.overthewire.org -p 2220 # paste the password you just found when prompted
Password
This is the password shown in my run; if yours differs, copy the one from your own terminal output.
7x16WNeHIi5YkIhWsfFIqoognUTyj9Q4
Troubleshooting
-
Garbled output? → Ensure you used single quotes and didn’t swap the two character sets.
-
Some
trversions prefer two calls:cat data.txt | tr 'A-Z' 'N-ZA-M' | tr 'a-z' 'n-za-m' -
Nothing prints? → Verify
data.txtisn’t empty and you’re in/home/bandit11.
Congrats 🎉 You decoded the ROT13 text and can now play as bandit12.
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


