OverTheWire Bandit Level 10 → 11 tutorial!!
Login
Log in as bandit10 using the password you just obtained from Level 9 → 10.
ssh bandit10@bandit.labs.overthewire.org -p 2220
# password: FGUW5ilLVJrxX9kMYMmlN4MgbpfMiqey
Why? Each Bandit level is a separate UNIX user. To solve 10 → 11, you must be the
bandit10user.
Task
The password for the next level is stored in data.txt, which contains Base64-encoded data.
A little bit of Theory
- Base64 is an encoding scheme (not encryption) that maps binary to 64 printable characters.
-
On Linux, use the
base64utility:- Decode:
base64 -d FILE - Encode:
base64 FILE
- Decode:
- Base64 output often ends with
=padding to reach a multiple of 4 characters.
Further reading:
Solution
-
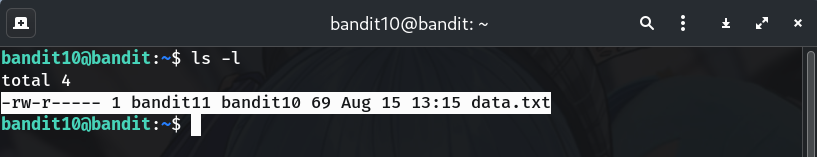
Confirm the file is present
ls -lWhy? Sanity check that
data.txtexists and you’re in the right place.
-
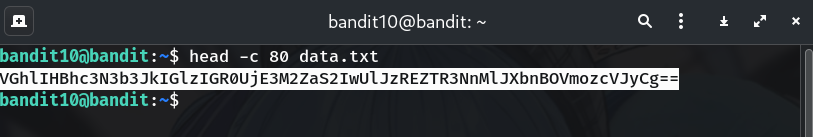
(Optional) Peek at the data — looks Base64
head -c 80 data.txtWhy? You’ll typically see A–Z, a–z, 0–9,
+,/, and maybe=padding.
-
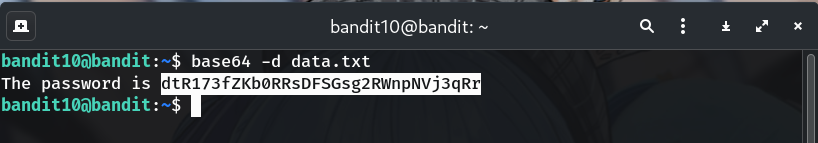
Decode the file with
base64 -dbase64 -d data.txtWhy? Decodes the Base64 text back to the original message containing the password.
-
Copy the password (no extra spaces/newlines).
-
Log into the next level (bandit11)
exit ssh bandit11@bandit.labs.overthewire.org -p 2220 # paste the password you just found when prompted
Password
This is the password shown in my run; if yours differs, copy the one from your own terminal output.
dtR173fZKb0RRsDFSGsg2RWnpNVj3qRr
Troubleshooting
base64: invalid input→ File may have wrapped lines oddly; trybase64 --ignore-garbage -d data.txt.- Empty/garbled output? → Ensure you didn’t include shell prompt text when copying; re-run
base64 -d data.txt. - Still unsure it’s Base64? →
file data.txtmay showASCII text; Base64 isn’t a “format”, just text—decoding is the test.
Congrats 🎉 You decoded the Base64 message and can now play as bandit11.
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


