OverTheWire Bandit Level 0 tutorial!!
Login
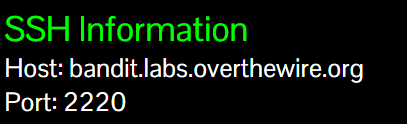
- This is the Bandit server login info (top-left on the official page): it shows the Host and Port you need.
ssh bandit0@bandit.labs.overthewire.org -p 2220
# password: bandit0
Task
Log into the game using SSH.
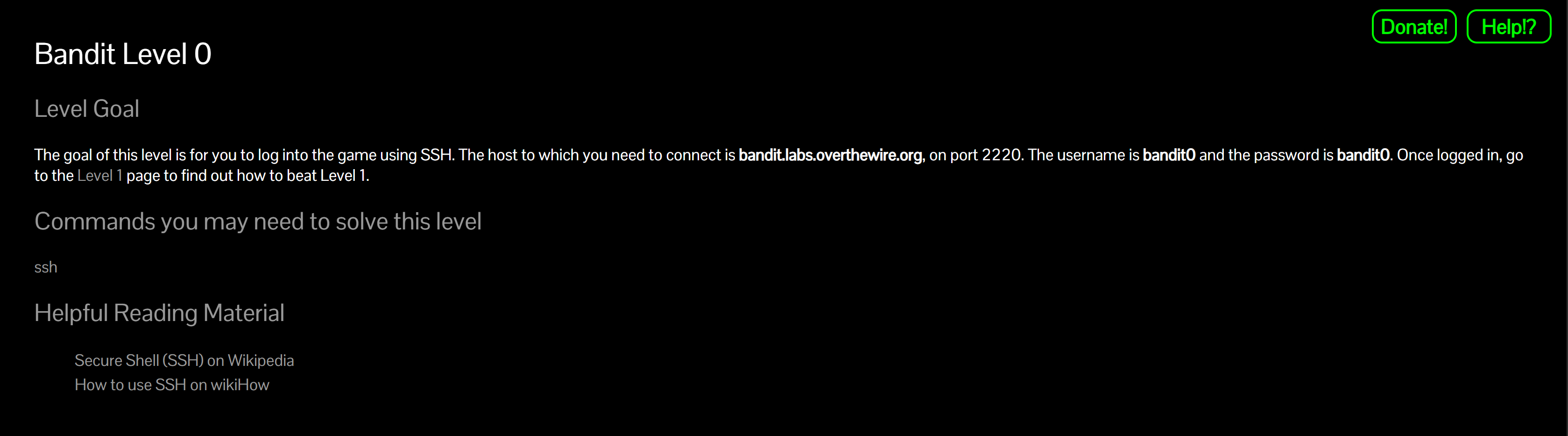
Your goal for this first level is simply to connect to the remote machine successfully.
A little bit of Theory
- SSH (Secure Shell Protocol) lets you connect securely to a remote machine over an encrypted channel.
-
The typical syntax is:
ssh <username>@<server> -p <port>Here,
bandit0is the username,bandit.labs.overthewire.orgis the host, and-p 2220uses the custom port 2220 instead of the default 22. - On Windows you can use WSL or PuTTY; on Linux/macOS just use the built-in Terminal.
- After a successful login, you land in the user’s home directory (shown by
~in the prompt).
Further reading:
Solution
-
Open a terminal Use Terminal (macOS/Linux) or WSL/PowerShell/PuTTY on Windows.
-
Run the SSH command:
ssh bandit0@bandit.labs.overthewire.org -p 2220Why?
sshstarts a secure session as user bandit0 to the host on port 2220 (Bandit’s custom port). -
First-time prompt: accept the host key You may see:
The authenticity of host ... can't be established. Are you sure you want to continue connecting (yes/no/[fingerprint])?Type
yes. Why? SSH stores the server’s fingerprint in~/.ssh/known_hostsso future connections can detect tampering (prevents man-in-the-middle). -
Enter the password (hidden input):
bandit0Why? SSH does not echo characters for security; just type and press Enter.
-
Verify you’re in as bandit0 You should see a prompt like:
bandit0@bandit:~$Optionally confirm:
whoami # should print: bandit0 pwd # should print: /home/bandit0 (or similar) -
Disconnect when done:
exitWhy? Cleanly closes the SSH session.
Troubleshooting quick tips
ssh: connect to host ... port 2220: Connection timed out→ Check your internet/firewall; make sure-p 2220is present.Permission denied→ Re-check the username (bandit0) and password (bandit0).Host key verification failed→ If you changed DNS/IP recently, remove the old entry in~/.ssh/known_hostsand reconnect.
Congrats 🎉 You’re now logged in as bandit0 and ready for the next level.
Thanks for reading!
Until next time — Otsumachi!! 💖☄️✨


